You’re Under Arrest: Funder Takes Extreme Measures to Counter Data Theft
An employee of Yellowstone Capital was arrested last month, according to a source who witnessed the events. At the company’s behest, local police entered Yellowstone’s Jersey City office and handcuffed a female employee who was believed to be engaged in the theft and misappropriation of financial data.
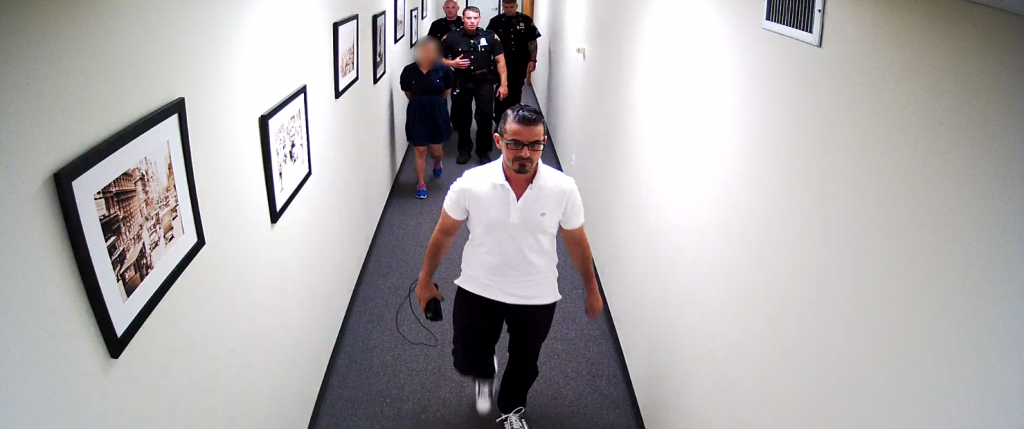
A spokesperson for Yellowstone would not comment on the events nor release the name of the accused. deBanked nevertheless obtained a photo of the individual being escorted out by police. We’ve blurred out her face to protect her identity. Several of those present, who spoke on the condition of anonymity, said that she had been employed by the company for several years.
When asked more generally about the risks of data leakage in the industry, Yellowstone Capital CEO Isaac Stern said that his company is operating on the edge of hyper vigilance. “Yellowstone is investing tons of time, money, and effort to prevent data theft,” Stern said. “We are doing everything in our power, everything, to address it, and we have even enlisted the assistance of an outside security firm.”
The incident does not stand alone. Last year, a man on Long Island pled guilty to attempted criminal possession of computer related material after being implicated in a merchant cash advance backdooring scheme.
Backdooring is industry jargon for when a broker submits a potential deal to a funder and that file ultimately leaks out to third parties whom the broker did not authorize to handle the information. Often times brokers will point their fingers at the funder for mismanaging data they suspect is escaping out the back door. Such accusations can be detrimental to a funder’s reputation not only with the broker community but also with customers they advance funds to. That’s why some funders are taking data security to new levels.
Greenbox Capital, for example, a funder in Miami, FL told deBanked back in March that their company designed proprietary software to monitor the actions of all users on their system, which allows them to know who clicked on what when, and for how long. They also developed algorithms to detect suspicious behavior and their security team receives an alert whenever it gets triggered. Greenbox had initially conducted a 90-day probe and discovered that two employees were stealing data. They don’t want that to ever repeat itself.
Using a cell phone to take pictures of confidential data may not help rogue employees evade detection, according to several funders who have said there are methodologies to spot this behavior but declined to explain what they are. And the risk of getting caught may not merely be termination, as evidenced by arrests that have taken place thus far. These funders say there have been other arrests over the last few years but that the companies did not want to draw attention to them.
Indeed, of the two backdooring-related arrests deBanked has reported on now, neither would officially confirm them.
“We take ISO information extremely serious,” Yellowstone’s Stern explained, lamenting that the value of deal data can inevitably foster rogue behavior, which they are constantly monitoring for.
Put another way, the personal information of a single performing client could be worth as much as $10,000 or more if it gets into the wrong hands. That’s because it could be used to offer that client a loan, advance or other service. The profit could come in the form of a commission, interest, RTR, a closing fee, or even something more nefarious like stealing their identity.
“We know about the pressure people face to illegally transmit data,” Stern said. “They think we don’t know, but we know the industry. Ultimately we will catch you.”
Last modified: April 20, 2019Sean Murray is the President and Chief Editor of deBanked and the founder of the Broker Fair Conference. Connect with me on LinkedIn or follow me on twitter. You can view all future deBanked events here.