MPR Advises MCA Companies to Perform Penetration Tests
The Merchant Cash Advance (MCA) industry is riding high from a stream of recent publicity and investor interest. Billions of dollars are pouring into the market and some companies are desperately trying to upgrade their software platforms to keep up with the growth. With more exposure comes new curiosity, and not all of it is positive.
There is no widely used software platform in the MCA industry, which is a good thing and a bad thing. It’s bad in the sense that each company has more or less created their own database system, increasing the odds that some companies will have security flaws. It’s good in the sense that if one company suffers some kind of breach, the method used should not be applicable across the entire industry.
Don’t worry, we’re not posting this to scare merchants. In fact, we don’t recall a single MCA firm ever having suffered a public data breach, a statistic unheard of in other industries. So why bring it up? As MCA firms collect more data and handle more money, the more likely they will become attack targets by hackers. The more valuable the stash, the more sophisticated the attacks. Major players like Heartland, TJX, and Global Payments have had sensitive information compromised on hundreds of millions of customers. The moral of the story? Prepare yourself as much as you can.
 If you think it can’t happen to you because your system was developed by a third party, you’re wrong. It’s time to get tested. A Penetration Test, as defined by wikipedia is:
If you think it can’t happen to you because your system was developed by a third party, you’re wrong. It’s time to get tested. A Penetration Test, as defined by wikipedia is:
a method of evaluating the security of a computer system or network by simulating an attack from malicious outsiders (who do not have an authorized means of accessing the organization’s systems) and malicious insiders (who have some level of authorized access).
Some may be inclined to compare a Pen Test to sitting in the waiting room of Student Health Services. You’re scared of what they might find and maybe you’d rather not know, but not getting tested at all is the worst thing you can do.
One such Pen Test was performed by an MCA firm months ago that had just purchased a customized software system from a third party. We will not name the firm or the software provider.
After a year of designing, testing, and writing fat checks to a prestigious group of software developers, the MCA firm had finally implemented a state of the art system that would propel them to the next level. After a month of using it, they asked a new hire to do some tests to make sure all of the basic features were working. The bells and whistles were decked out to the nines but no one had tested the easy things like going through the motions of resetting their password if they forgot it.
The new hire noticed something slightly off with the basics and reported his findings to the executives. Interested, but not really worried, they gave him permission to act as if he were a disgruntled employee. Turnover was high in the telemarketing department and there was occasionally a person that would shoot off a couple of dumb e-mails on their way out. But now with a system in place, could they do real damage?
The disgruntled employee test was really a simple Pen Test and this firm is eternally thankful that it performed one. Within 7 minutes, the new hire was able to access and modify every piece of data in the system. He was able to exert administrative power without having administrative level access. The worst part of what he did? There was no way to prevent against this mess because of how the software was coded. The best part of what he did? It was only a test and all modifications were immediately reversed.
It took a long time for the MCA firm to take a corrective course of action. Whether they ended up patching the software or tossing it altogether, we won’t say. What’s important is that they were able to identify these flaws on their own and early on. Many companies in this industry have long-term funding projections that exceed $1 billion. At that size, there will be much more to worry about than disgruntled employees. The bad guys will be lined up around the block in cyberspace trying to get in. SQL injections, buffer overflow attacks, DDoS Attacks, and much more will be lighting up those systems on a daily basis. Most MCA account reps advise their merchants about PCI compliance, but today we’re reminding you to take your own advice.
Resources:
In-house Penetration Testing for PCI DSS
Penetration Testing Guide and Samples
Security Assessment-Penetration Testing and Vulnerability Analysis
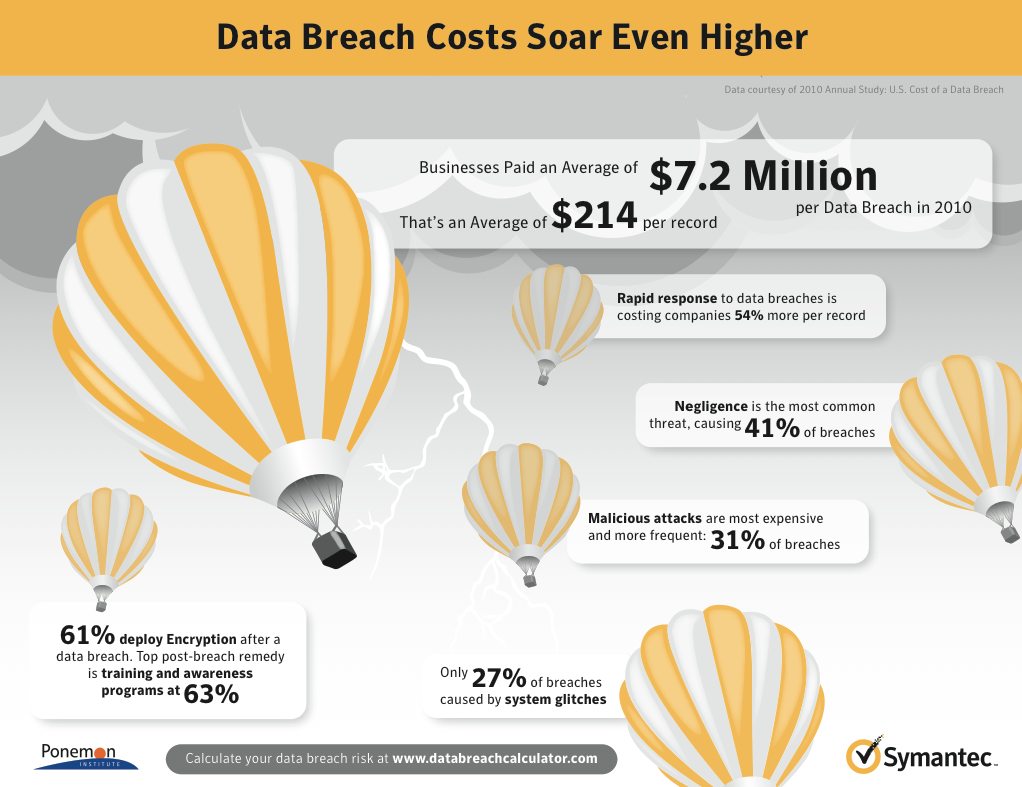
Cost of a Data Breach
Estimate Your Risk Exposure
Global Payments Breached
Pass it on.
– Merchant Processing Resource
https://debanked.com
Sean Murray is the President and Chief Editor of deBanked and the founder of the Broker Fair Conference. Connect with me on LinkedIn or follow me on twitter. You can view all future deBanked events here.